The Push: May 12th, 2026
Smarter internet tunnels, spare-phone video rigs, and document maps that help AI actually find the right page
Hysteria: Proxy Performance Became Product
github.com/apernet/hysteria | License: MIT
Hotel Wi-Fi, airport captive portals, overloaded mobile networks, hostile national filters, the network fails in different ways depending on where you are. That is exactly why a lot of proxy tools feel disappointing in practice. They benchmark well on a clean connection, then fall apart when packets drop, latency spikes, or traffic gets flagged as suspicious. Hysteria is interesting because it treats bad networks as the default condition, not the exception. Honestly, that framing matters more than raw speed claims.
The Drop: Built for the Internet You Actually Get
Anyone who has used a proxy outside a pristine home fiber setup knows the annoyance. One service loads instantly, another stalls forever, video calls glitch, UDP-heavy apps break, and the workaround stack gets ridiculous fast. Traditional tools often assume the network is merely slow. Hysteria is solving for something messier, where the network is lossy, inconsistent, and sometimes actively trying to detect or throttle what you are doing.
That distinction matters because censorship and poor connectivity increasingly blur together. A university network, an airport ISP, and a state firewall can all produce the same user experience: random failures that are hard to diagnose and harder to route around. Hysteria steps into that gap as a censorship resistant proxy that also acts like a practical performance tool. Not just unblock-the-web software, but a system designed for unreliable conditions where TCP retries become a tax and standard VPN behavior becomes painfully obvious. The frustration driving the project is simple: if staying connected requires protocol trivia and constant tweaking, the software has already lost.
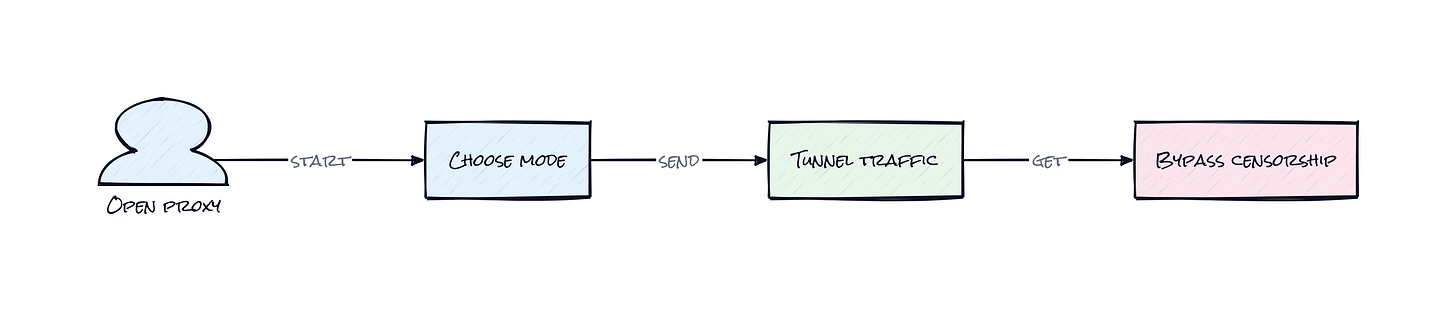
The Stack: Go, QUIC, and a Lot of Edge Cases
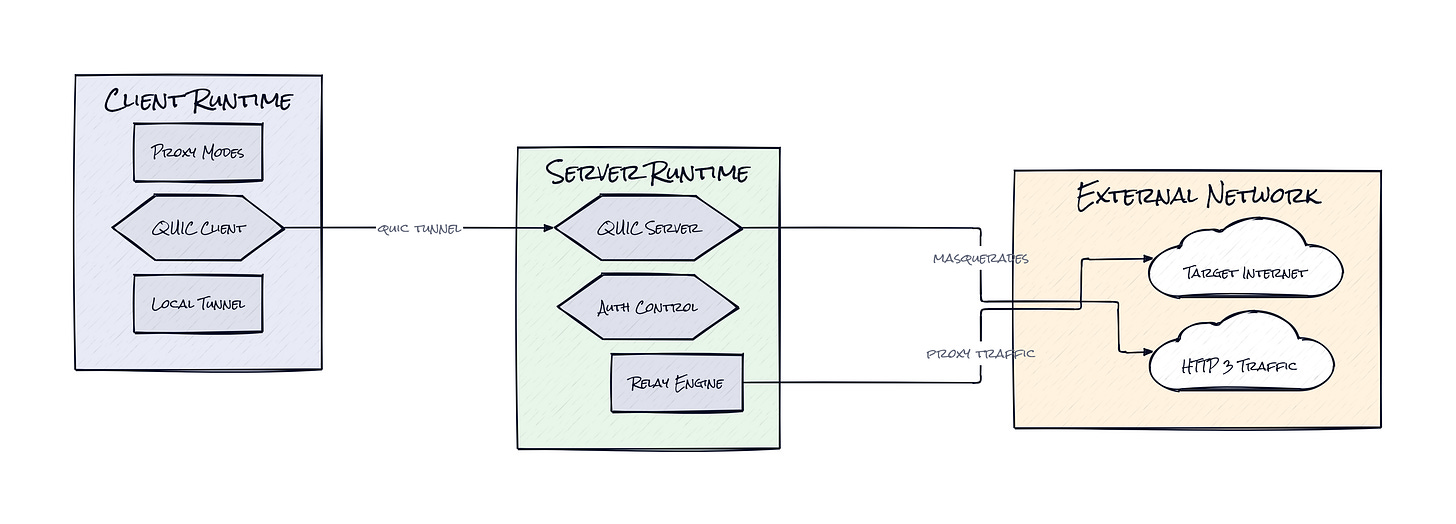
Under the hood, Hysteria is built in Go, with a custom transport layer centered on QUIC, the same protocol family behind HTTP/3. Around that core sits a broad access layer, e.g. SOCKS5, HTTP proxying, TUN mode, transparent proxying, forwarding, TLS automation through CertMagic, and optional masking features that help traffic blend in.
The Sauce: HTTP/3 as Camouflage, QUIC as Control Plane
What makes Hysteria stand out is its choice to build around customized QUIC protocol behavior while presenting traffic that can resemble ordinary HTTP/3 traffic. That combination does two jobs at once. QUIC gives the system finer control over congestion, packet loss, and multiplexing on sketchy networks. HTTP/3 camouflage raises the blocking cost for anyone trying to identify and kill the connection without also breaking legitimate modern web traffic.
That is a smart architectural bet because detection pressure has moved up the stack. Plenty of networks no longer just block obvious ports or old-school VPN signatures. They inspect patterns. Hysteria responds by making transport design part of the product, not a buried implementation detail. The server side also exposes a surprisingly broad operating model: masquerade support can front traffic behind a normal-looking site or service, while outbounds let operators define where traffic exits and how policy gets applied. Add built-in auth, traffic stats, access control, and certificate automation, and the repo starts to look less like a single proxy binary and more like a compact networking platform.
The interesting part is not that Hysteria supports many modes. Plenty of projects do. The interesting part is that one transport core can feed multiple client behaviors without forcing the operator into one deployment philosophy. That flexibility creates resilience. If one access pattern gets noisy or blocked, another can ride on the same architecture with less reinvention. That is how open source infra earns staying power.
The Move: A Connectivity Hedge, Not Just a Tool
Founders, distributed teams, and anyone shipping products across regions can use Hysteria as a strategic fallback layer. Set it up on a cloud instance, attach a domain, enable TLS, and route traffic through whichever mode fits the moment, e.g. browser proxying for quick access, TUN for full-device routing, or forwarding for a specific app that keeps failing on a hostile network. The repo is broad enough to serve both personal connectivity and lightweight team infrastructure.
More interestingly, Hysteria can function as risk management. If a product depends on overseas APIs, remote admin access, or customer support staff working across restricted networks, connectivity becomes an operational dependency, not a side issue. Hysteria gives teams a way to test alternative egress paths, benchmark degraded links, and maintain access without buying into a heavyweight enterprise networking stack on day one. That matters for startups expanding into Southeast Asia, the Middle East, or Africa, where network quality and filtering can be wildly uneven. The advantage is not just access, it is continuity. When the default route gets flaky, the business does not have to stop.
The Aura: Reliability Changes Expectations Fast
People stop treating the internet as a fixed utility once tools like Hysteria become normal. Connectivity starts to feel negotiable, tunable, even portable. That changes behavior. Remote work looks less geographically fragile, global products look less dependent on the luck of local infrastructure, and users get less willing to accept “network error” as a final answer.
There is also a quiet political layer here. Software that makes degraded or filtered networks usable does not just restore speed, it restores agency. That is the deeper appeal. Better routing becomes a way to preserve choice when institutions, infrastructure, or incumbents would rather narrow it.
The Play: Infrastructure PMF Hides in Distribution
From a VC lens, Hysteria looks less like a pure 0-to-1 category creator and more like an exceptionally strong wedge in the large, messy market spanning VPNs, proxy infrastructure, edge networking, and censorship circumvention. TAM is easily multi-billion if the lens includes consumers, remote teams, privacy-focused operators, and regional infra providers. The repo’s 20,110 stars, active docs, broad mode support, and long-tail deployment flexibility are decent open source PMF signals, though the moat is still mostly execution speed and operator trust, not hard defensibility.
Winners:
Tailscale: More demand for flexible private connectivity compounds because users educated by Hysteria increasingly expect network paths to be software-defined, not fixed by the ISP.
Cloudflare: More traffic management and security demand accrues because resilient routing, masking, and edge termination become standard expectations for globally distributed apps.
Akamai: More enterprise spend shifts toward adaptive edge delivery because network reliability and traffic shaping start looking like core product features, not back-office plumbing.
Losers:
Mullvad Browser: More user attention drifts toward transport-level reliability tools, which erodes differentiation for privacy products that do not solve degraded network performance directly.
ExpressVPN: More margin pressure shows up because open, configurable proxy stacks make premium consumer VPN pricing harder to justify for power users and small teams.
Cisco: More of the connectivity stack gets unbundled into software-first, operator-friendly components, which makes appliance-heavy network strategy feel slower and less adaptable.
tl;dr
Hysteria turns flaky, filtered internet access into an engineering problem instead of a dead end. The smart move is pairing QUIC-based performance control with HTTP/3-looking traffic, which makes blocking harder and bad networks more usable. Worth a look for remote teams, global startups, and anyone treating connectivity as operational infrastructure.
Stars: 20,110 | Language: Go