The Push: April 24th, 2026
Open-source picks for vuln triage, self-hosted password sanity, and faster MoE token traffic
Osv Scanner: Security Debt Needs Receipts
github.com/google/osv-scanner | License: Apache-2.0
A dependency alert lands in Slack, someone pastes a CVE link, and the next hour disappears into archaeology. Which package pulled it in, does the affected version actually exist in production, and is this a real problem or another scanner crying wolf? That mess is exactly why Osv Scanner feels timely. Security tooling has had a trust problem for years, not because teams hate scanning, but because noisy results turn every alert into a mini research project. That is expensive.
The Drop: When Vulnerability Feeds Become Homework
Plenty of teams already know they have vulnerable packages. The pain starts one layer deeper: mapping a public advisory to the specific dependency graph, lockfile, container layer, or vendored code sitting inside a real project. Traditional scanners often dump a pile of findings without enough context to act, which means engineers still have to manually trace the blast radius and decide whether a fix is worth the churn.
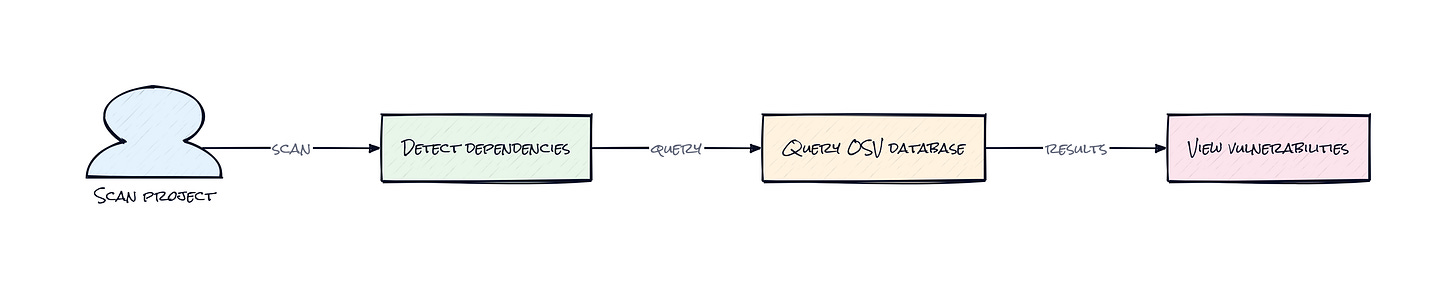
Google’s OSV.dev database gave the ecosystem a cleaner vulnerability source, built around machine-readable version ranges instead of messy prose. But a database alone does not solve the workflow problem. Someone still needs to connect package manifests, resolved dependencies, operating system packages, and container artifacts to those advisories in a way that produces answers, not just data.
Osv Scanner exists because security teams are tired of paying the false-positive tax. Honestly, the frustration is not just “too many bugs.” It is too many alerts with weak explanation, weak prioritization, and weak remediation guidance. That is how security becomes everyone’s side quest instead of a shipping constraint.
The Stack: Go Built for Cross-Ecosystem Digging
Under the hood, Osv Scanner is written in Go, which makes sense for a fast portable CLI that needs to inspect lots of project types. It sits on top of OSV-Scalibr, Google’s extraction layer for dependencies and artifacts, and pulls advisory and package intelligence from OSV.dev and deps.dev for vulnerability, license, and remediation context.
The Sauce: A Scanner That Connects Artifacts to Reality
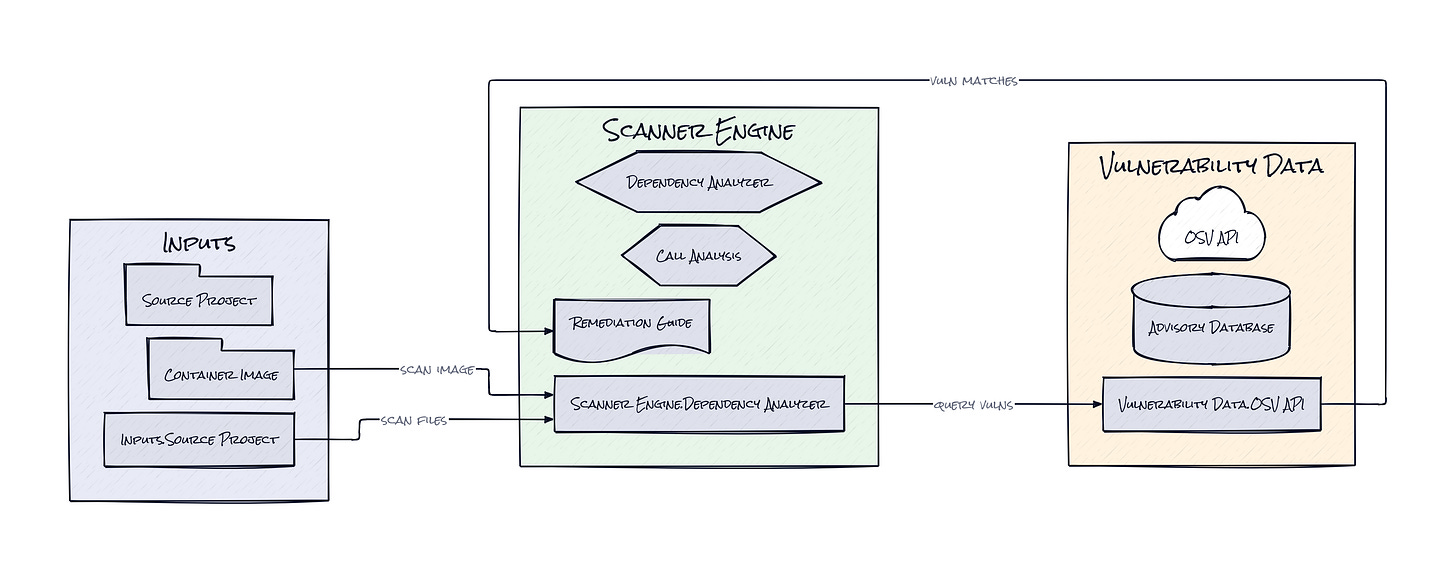
What makes Osv Scanner interesting is its decision to act less like a keyword matcher and more like an evidence engine. The repo combines OSV.dev, a normalized vulnerability database with precise affected-version data, with OSV-Scalibr, an extraction layer that identifies dependencies across source trees, lockfiles, operating system packages, and container images. That sounds straightforward, but it changes the product shape in a big way.
Instead of treating security scanning as “grep your repo and compare against a list,” Osv Scanner builds a richer picture of what software is actually present. That includes recursive source scanning, layer-aware container inspection, offline database mode, and even Guided Remediation, which suggests upgrade paths based on factors like dependency depth, severity, and return on investment. That last part matters because the hard problem in dependency security is rarely detection. It is deciding which upgrade gets the biggest risk reduction with the least breakage.
There is also a quiet but important architectural choice around source analysis. For supported ecosystems, Osv Scanner can use call analysis to determine whether vulnerable code paths are actually referenced. That trims down the classic “technically vulnerable, practically irrelevant” noise that makes security dashboards unbearable. Add the open advisory model, where vulnerability records come from authoritative upstream sources and remain machine-readable, and the result is a scanner that feels closer to supply chain observability than checkbox compliance. That is the clever bit.
The Move: Turn Security Triage Into Decision Support
Security leaders could drop Osv Scanner into CI and get immediate value, but the smarter move is broader. Run it across application repos, base container images, and internal templates, then use the results to build a ranked dependency risk program. The goal is not another red dashboard. The goal is knowing which packages repeatedly create upgrade pain, which teams inherit risky transitive chains, and which base images are quietly spreading exposure across the company.
Product and platform teams can use offline scanning for regulated environments, pair license scanning with procurement policy, and test Guided Remediation on high-churn ecosystems like npm where dependency sprawl gets ugly fast. Container support is especially strategic because base image risk tends to multiply silently across services.
Founders and smaller teams get a different advantage. Osv Scanner gives startup engineering orgs a credible security baseline without buying a giant enterprise suite on day one. That matters in sales cycles. Enterprise customers increasingly ask for software supply chain answers early, and “here is the open scanner, the database, and the remediation workflow” sounds a lot stronger than “someone checks GitHub alerts sometimes.” Practical beats performative.
The Aura: Trust Starts With Specificity
Engineers change behavior when alerts stop feeling arbitrary. A result tied to an actual dependency graph, a real container layer, or a likely-used code path is easier to respect, easier to fix, and easier to budget time around. That sounds small, but it changes the emotional contract between builders and security.
Open, machine-readable vulnerability intelligence also nudges expectations upward. People start assuming security findings should be explainable, portable, and automatable, not trapped inside a vendor dashboard. That expectation is healthy. It treats software risk less like institutional folklore and more like shared infrastructure.
The Play: Open Vulnerability Intelligence Gets Productized
This looks less like a pure 0-to-1 category creation and more like a better mousetrap in a massive existing TAM, software supply chain security, developer tooling, and enterprise compliance budgets are already huge. The bullish angle is PMF through trust: open data provenance, actionable remediation, and broad ecosystem coverage reduce CAC because the repo itself becomes the top of funnel. With 9,334 stars, Google branding, and clear community adoption, Osv Scanner shows credible pull, but moat comes more from execution speed, integrations, and workflow stickiness than from raw defensibility.
Winners:
Semgrep: Distribution gets stronger because open, explainable dependency findings pair naturally with code and policy scanning, increasing expansion revenue without owning the whole vulnerability database stack.
Snyk: Enterprise upsell gets easier if the market keeps caring about remediation workflows and cross-artifact visibility, because paid governance can sit on top of the same pain Osv Scanner makes legible.
GitHub: Platform gravity increases as developers expect dependency risk, advisories, and remediation suggestions to live where code review already happens.
Losers:
Endor Labs: Positioning around differentiated supply chain insight gets pressured as open tooling closes the gap on baseline dependency visibility, making premium pricing harder to justify early.
Aqua Security: Container security margins get squeezed when buyers realize a meaningful slice of image and package risk detection can come from open components with decent accuracy.
Synopsys: Legacy scanner economics erode as procurement teams question why opaque databases and heavyweight deployments should command premium spend for increasingly standardized vulnerability intelligence.
tl;dr
Osv Scanner turns open vulnerability data into something teams can actually act on, across source repos, lockfiles, containers, and licenses. The smart part is the architecture: precise advisory data plus artifact-aware scanning plus remediation guidance. Security teams, platform groups, and startup founders selling into enterprises should look.
Stars: 9,334 | Language: Go