The Push: April 20th, 2026
DNS ad-blocking, WiFi that senses breathing, and a live map of markets, news, and global chaos
Pi Hole: Ad Tech’s Tiny Nemesis
github.com/pi-hole/pi-hole | License: Other
Three devices into a hotel stay, the pattern gets old. The TV has banner ads, the phone app has autoplay junk, the tablet browser feels bloated, and every fix is per-device whack-a-mole. Browser extensions help, until they don’t. Mobile apps ignore them. Smart home gear definitely does. Pi Hole attacks that annoyance at the network level, which is why it has stayed relevant for a decade. This is not another privacy tool asking for trust in some cloud service. It is your own box, answering DNS questions and quietly saying, nope, not to a huge chunk of the internet’s junk.
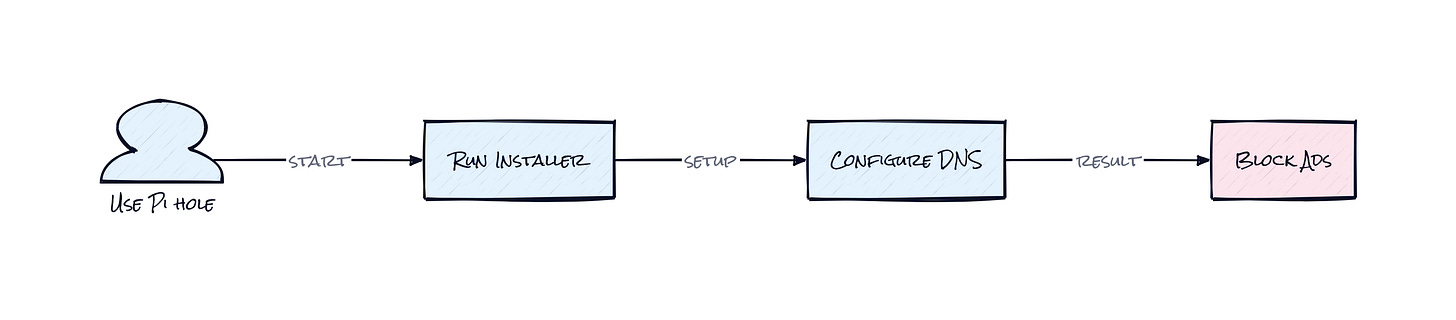
The Drop: Blocking Ads Before Apps Wake Up
Plenty of ad blockers make a seductive promise, install one thing and browsing gets cleaner. Then reality shows up. The browser extension only works in the browser. The VPN app drains battery. The “private DNS” setting breaks something random. Meanwhile, connected TVs, game consoles, thermostats, and family devices keep calling home to trackers and ad networks because nobody is going to configure each one manually.
Pi Hole exists because the actual choke point was never the app interface. It was DNS sinkhole logic, intercepting requests for known ad and tracking domains before a device can even connect. That sounds simple, but the frustration it solves is bigger than ads. Network clutter, slower page loads, telemetry spam, weird smart TV behavior, all of that often starts with domain lookups you never asked for. The appeal here is broad coverage with one decision. Point the router at Pi Hole, or let Pi Hole handle DHCP, and suddenly every device on the network inherits the same rules. No extension store. No app install. No begging family members to change settings.
The Stack: Bash With Teeth
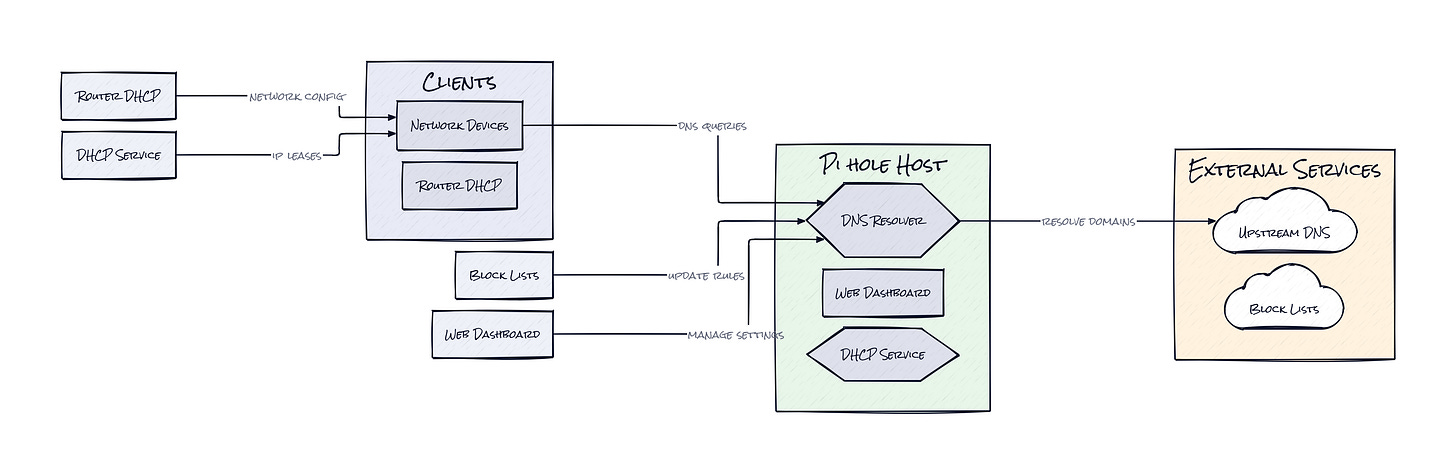
Under the hood, Pi Hole is mostly Shell scripts orchestrating installation, updates, list management, and system integration on Linux. The core engine leans on FTLDNS, a purpose-built DNS daemon with stats and API support, plus dnsmasq-style local resolution behavior and an optional web dashboard for management.
The Sauce: DNS as Product Surface
Network products usually lose people in configuration screens. Pi Hole wins by turning Gravity into the center of the system, a consolidated blocklist database that converts scattered community lists, allowlists, deny rules, and regex filters into one queryable source of truth. That sounds mundane, but architecturally it is the reason the project works for normal households and obsessive tinkerers at the same time.
Every device on the network asks for domain resolution. Pi Hole sits in that path and answers locally when a domain should be blocked, or forwards the request upstream when it should pass. The important part is not just “block ads with DNS.” The interesting part is that policy lives in one place, at the resolver layer, where browsers, apps, TVs, and IoT devices all become equal citizens. That is a cleaner control plane than client-side blockers, which fragment rules across plugins and operating systems.
Then there is FTL, the high-speed daemon that folds logging, cache awareness, and stats into the same layer that serves DNS responses. That combination matters because visibility and enforcement share context. Pi Hole can show top blocked domains, per-client query behavior, and cache hit patterns without bolting on some external observability stack. Honestly, this is why the project aged well. It is not a one-off script. It is a local network policy engine packaged like a hobbyist tool, with enough telemetry to feel surprisingly professional.
The Move: Turn Privacy Into Default Settings
Households, coworking spaces, indie cafés, small studios, and even founder apartments can get immediate value by putting Pi Hole between devices and the wider internet. The obvious win is ad blocking, but the more strategic use is standardization. One network policy means fewer support headaches, faster browsing on constrained devices, and a live map of what hardware is actually talking to outside services.
Small teams can also use Pi Hole as an early warning layer. A prototype smart device phoning home to twelve analytics endpoints? A conference room TV hammering sketchy domains? A kid’s tablet app making hundreds of lookups per hour? Pi Hole surfaces that behavior without expensive enterprise tooling. That creates operational clarity, not just cleaner screens.
Founders and product people should notice another angle: Pi Hole is a cheap way to test what parts of an experience truly depend on third-party ad, analytics, or recommendation services. Run a network through it for a week and patterns appear fast. Which apps degrade gracefully, which ones break, which services are absurdly chatty. That kind of ambient intelligence is useful when privacy promises, performance budgets, and vendor risk are no longer side quests.
The Aura: Control Feels Different at Home
People get used to software making unilateral choices, what loads, what tracks, what pings a server every few seconds. Pi Hole restores a different expectation: the network owner gets a vote. That psychological shift matters because it changes passivity into selective trust. Devices stop feeling like sealed consumer objects and start feeling inspectable again.
Home infrastructure used to be invisible unless something broke. Projects like Pi Hole make invisibility less acceptable. Once query logs and block rates are visible, “smart” starts to look a lot like “chatty.” That awareness tends to stick.
The Play: Consumer Privacy Infrastructure, Not Just Ad Blocking
This looks less like a 0-to-1 category and more like a brutally good wedge into a large existing TAM around privacy, parental controls, home network management, and SMB security. PMF signals are obvious: 56,954 stars, long-lived community support, forks, docs, and sustained relevance across hardware cycles. The moat is not proprietary data. It is distribution through trust, habit formation at the network layer, and execution around reliability. Once a home or office sets DNS policy centrally, switching costs rise because the behavior becomes embedded in everyday connectivity.
Winners:
Tailscale: More secure home and small-office networking becomes easier to bundle with local DNS control, and that compounds into higher LTV as users stack private infrastructure tools.
eero: Premium router software gets more valuable when users expect network-level policy and visibility, pushing eero closer to a higher-margin control plane for the connected home.
Cloudflare: Consumer trust in DNS as a product surface expands demand for upstream resolvers, secure DNS, and adjacent filtering services that plug into more opinionated local setups.
Losers:
Nodal: Consumer privacy products built as one-off app utilities lose oxygen when network-wide blocking solves the problem more completely and with lower ongoing CAC.
Life360: Family safety software that depends on broad device permissions and passive background data collection faces more friction as households get used to filtering and inspecting outbound behavior.
Alphabet: Ad-supported surfaces outside the browser, especially on Android apps and connected TV endpoints, see incremental erosion when more households normalize resolver-level blocking.
tl;dr
Pi Hole turns a cheap Linux box into a network-wide ad and tracker filter by sitting at the DNS layer, where every device has to ask permission before loading junk. What is clever is the centralized policy model plus built-in visibility. Anyone running a busy home, office, or device lab should look.
Stars: 56,954 | Language: Shell